New Shlayer Trojan infects millions of macOS devices

Cyber criminals are always looking for interesting means to affect users and exploit their ignorance towards cybersecurity. MacOS is usually considered to be better than Windows machines when it comes to cybersecurity, however with the latest malware named ‘Shlayer’ aTrojan, macOS users could become victim to adware threats.
What is macOS Shlayer Trojan attack?
Shlayer Trojan infects macOS devices in two phases, in the first phase the Shlayer Trojan enters user device through malicious programs that have been downloaded by the users from third party sites, once the user installs the malicious programs, the Shlayer inside these programs will install itself into the device using the malware distribution system. In the second phase, Shlayer installs multiple adware that are being sponsored by many partners who will be benefited through this Trojan distributed adware campaigns. And there are around 1000 entities who are actively distributing this Shlayer Trojan (Trojan-Downloader.OSX.Shlayer.a ) through their networks.
Even trusted websites like Youtube and Wikipedia are found distributing this malware, so macOS users are requested to stay alert while downloading programs. It is believed this Trojan has infected millions of macs already.
History macOS Shlayer Trojan attacks
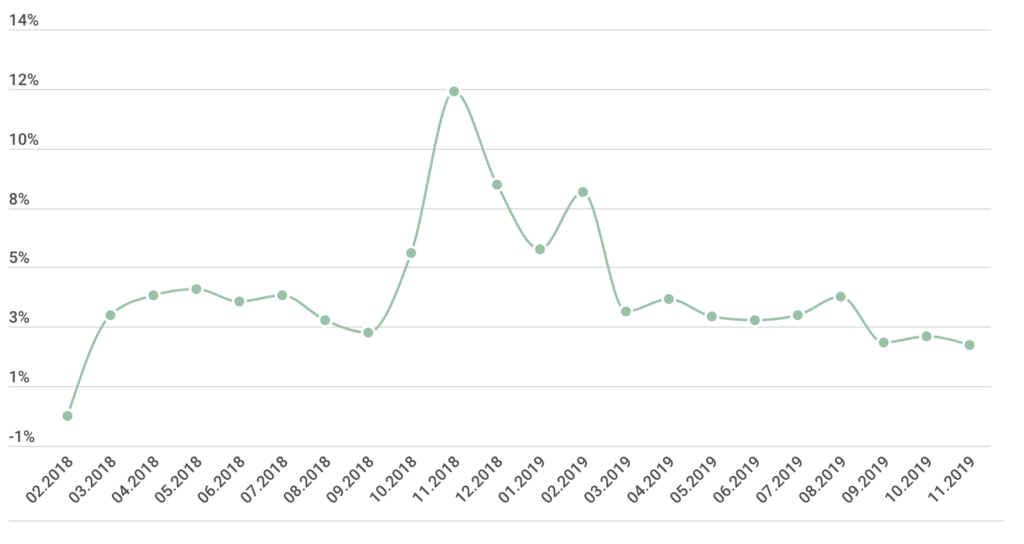
This Trojan isn’t new to the cyber world, Kaspersky’s report shows the Trojan has been around for a while from 2018, and is created using the Python scripts. However, unlike other malware this Trojan hasn’t evolved much, displaying how effectively the current version is helping the cyber criminals. This Shlayer Trojan also had bash-based cousins in the web.
How should users mitigate against Shlayer Trojan?
sers need to be aware of their browsing practices, and ensure they do not download any programs from untrusted websites, even while downloading applications from trusted websites, its vital to check for malicious files and extensions. Users can also use anti-virus applications to identify the threat, making sure their AV has received the latest definitions.
Users should also look out for redirection when they click on a legitimate links, these could be fake links that redirect the users to websites where the Shlayer Trojan gets downloaded automatically.Users are also requested to checkout Adobe Flash Player updates and redirection which is found to be the primary breeding grounds for this Shlayer Trojan.
Kaspersky, has showcased the entire Shlayer Trojan Attack in their SecureList Blog, please read through it for details.





