James Webb Telescope Image malware hidden and deployed by hackers

Security analysts have identified a new malware campaign ‘GO#WEBBFUSCATOR’ that works on malicious documents, phishing emails, and space images form the James Webb telescope to distribute malware.
The coding of the malware is done in Golang, a programming language that is recently popular among the attackers as it is compatible with Windows, Mac and Linux devices with increased resistance against reverse engineering and analysis.
Security researchers at Securonix have discovered a campaign where the attackers are dropping payloads and the antivirus tools aren’t marking them as malicious.
Modus Operandi behind James Webb Telescope Image Malware
The attackers start with a phishing email with a malicious document attached to the email, “Geos-Rates.docx” that downloads a template file. The file has an VBS macro that auto-executes if macros are enabled.
Later, the code downloads a JPG image from a remote source, decode it into an EXE using certutil.exe and deploys it into the environment.

When this image is viewed under right security filters, it shows the galaxy cluster SMACS 0723 published in July 2022. And, when the same is analyze further using text editor, the image reveals additional code disguised as an certificate that has the Bas64-encoded payload which modifies into the malicious 64-bit EXE file.
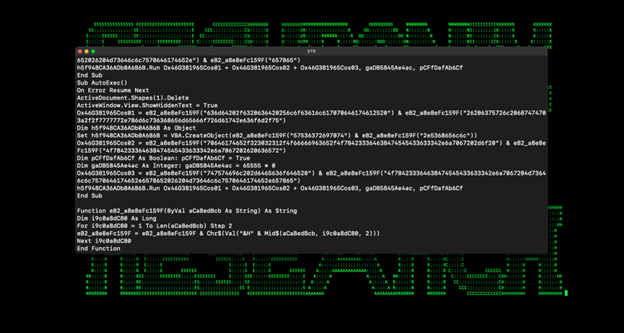
The payload is further obfuscated using ROT25, while the binary uses XOR to disguise the Golang from the security detectors.
Capabilities of the James Webb Telescope Image Malware
The James Webb Telescope malware duplicates itself to ‘%%localappdata%%\microsoft\vault\’ with a new registry key. After execution, the James Webb Telescope Image malware establishes a DNS connection to the C&C server and shares encrypted queries with it.
The C&C server responds to the queries in time intervals, altering the nsloopup timeout, or by sending our commands to execute through the Windows cmd.exe tool.
The Securonix researchers also found out that the malicious actors behind this James Webb Telescope Image malware are running arbitrary enumeration code on the test devices before deploying it to several other endpoints. The security researchers mentioned that the domains used behind the distribution were registered recently with the oldest one on May 29, 2022.
With the network and host-based IoCs provided by Securonix, network and system administrators should be able to identify and act on these threats.
Subscribe to our newsletter for daily alerts on cyber events, you can also follow us on Facebook, Linkedin, and Twitter. You can reach out to us via Twitter/ Facebook or mail us at admin@thecybersecuritytimes.com for advertising requests.








