FIN7 actors sent Malicious USB drives to US companies with ransomware

The FBI has identified malicious USB devices that are sent to US companies in recent months with the motive to infect the company networks with malware and further payload drops. The group behind this malicious USB operation is found to be FIN7 actors, the ones behind BlackMatter and Darkside ransomware.
As per the FBI report, several packages with USB drives have been shipped to US companies including defense, insurance and transportation industry. The delivery has been made via United Parcel Service and United States Postal Service. The packages came in two variants, one with US Department of Health and Human Services name on it, with few COVID-19 guidelines and a USB drive.
The other one was disguised as an Amazon Package with gift decorations, thank you message, gift card and USB drive. One common thing between these two packages is that the USB drive was from the LilyGo brand.
FIN7 actors sent USB drives that can install a ransomware
Once the recipients plug-in these USB drives into their devices, a BadUSB attack is initiated. A BadUSB attack is a security attack which infects the devices by reprogramming the USB drive with malicious software. With these malicious programs the actors can download multiple payloads into the device and make them act as a backdoor for further infiltration. Once the actors gain the admin privileges for a system they continue their attack by spreading the malware laterally across the network affecting other peer devices.
After successful lateral distribution the FIN7 actors employed multiple tools to deploy REvil and BlackMatter ransomware. The tools include Cobalt Strike, Metasploit, Carbanak, TIRION, DICELOADER, GRIFFON, and Carbanak.
FIN7 actors sent the USB drives to US defense organization
In November 2021, the FIN7 actors sent the USB drives to US defense organization with the Amazon package details mentioned above. It is to be noted that the FBI already have warned US companies in March 2020 regarding FIN7 actors and their intent, so this will be the second alert sent out by the FBI.
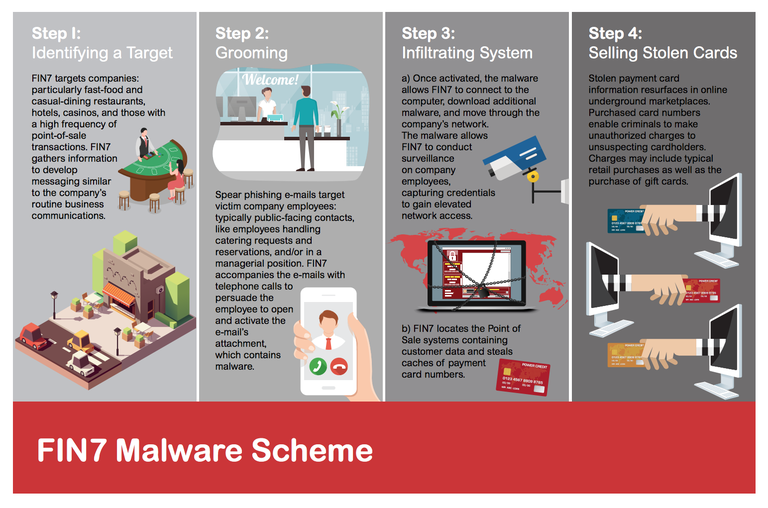
The details of the delivery package with images of the LiliGo brand, the COVID-19 guidelines and Amazon thank you message is available in the InfraGard Portal which companies can access after registering themselves for alerts and get a heads up on FIN7 actors and their attacks. The FBI has been warning companies for a long time about FIN7 actors, here is one such detailed modus operandi breakdown from the FBI that was published in 2018.
Subscribe to our newsletter for daily alerts on cyber events, you can also follow us on Facebook, Linkedin, Instagram, Twitter and Reddit.
You can reach out to us via Twitter or Facebook, for any advertising requests.





