RansomBoggs ransomware targets Ukrainian Organizations powered by Sandstorm

A new set of ransomware attacks under have been identified targeting Ukraine and it has seemed to have been coming from the Russian military threat group called Sandworm.
Slovakian software company ESET first identified this wave of ransomware attacks, has named the ransomware to be RansomBoggs, and mentioned that this ransomware is found in several Ukrainian network recently.
The ESET researchers said “While the malware written in .NET is new, its deployment is similar to previous attacks attributed to Sandworm.
There are similarities with previous attacks conducted by Sandworm, a PowerShell script used to distribute the .NET ransomware from the domain controller is almost identical to the one seen last April during the Industroyer2 attacks against the energy sector.”
Modus Operandi of RansomBoggs ransomware
RansomBoggs ransomware is deployed as a payload using a PowerShell script called POWERGAP and it is the same one behind the CaddyWiper malware that was deployed against Ukraine in March 2022.
After successfully deployed into a network, RansomBoggs ransomware encrypts files using a AES-256 with CBC mode using a randomly generated encryption key and it appends with .chsch extension to encrypt file extensions.
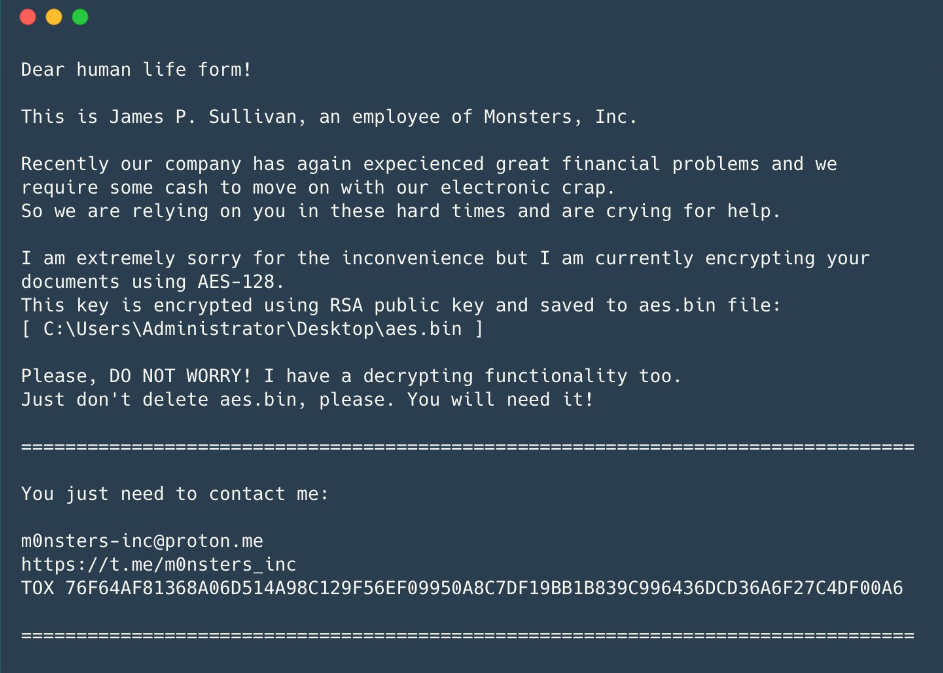
Based on the RansomBoggs ransomware version, the RSA public key can either be hardcoded inside it or be given as an argument. On the infected systems, the RansomBoggs ransomware delivers a ransom note impersonating James P.Sullivam, a character from the Mosters Inc movie.
Furthermore, a few weeks before Microsoft also mapped the Sandworm cyber-espionage group to Prestige ransomware attacks that targeted logistics industry in Poland and Ukraine.
RansomBoggs ransomware and Sandworm hackers
Sandworm is an elite group of Russian hackers that have been active for more than 20 years now with being a part of Unit 74455 of the Russian GRU’s Main Center for Special Technologies.
Sandworm has been involved in the KillDisk wiper attacks hitting Ukraine caused blackouts in 2015 and 2016.
Moreover, it is believed that Sandworm were the ones behind the development of NotPetya ransomware that hit the world in June 2017 right after the WannaCry incident.
Russian hackers have been heavily involved in cyberattacks on Europe and other countries, stealing 50 million passwords recently.
Also, Russian Killnet entity launched a DDOS on European Parliament this week and here the Russian malicious bodies are on to Ukrainian organizations again.
Subscribe to our newsletter for daily alerts on cyber events, you can also follow us on Facebook, Linkedin, and Twitter.
You can reach out to us via Twitter/ Facebook or mail us at admin@thecybersecuritytimes.com for advertising requests.








