Chinese APT41 hackers breached into Six U.S. State Organizations

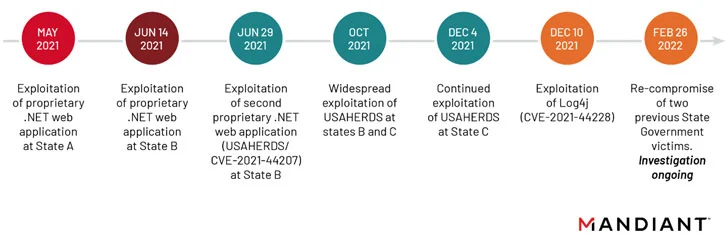
The Chinese APT41 hackers, a state-sponsored threat entity of China had breached into at least six U.S state government environment from May 2021 to February 2022 by redefining their attack vectors and exploiting the existing vulnerabilities in the victim’s web applications.
Who are Chinese APT41 hackers?
A state-sponsored hacking group that is hacking organizations across the world and mostly US with strong ties to China, classified as Advanced Persistent Threat (APT), as named by the US Department of Justice is called Double Dragon a.k.a APT41. They also go by other names like Barium, Wicked Panda, Wicked Spider, Bronze Atlas, Blackfly, Red Kelpie and TG-2633.
On January 2022, a similar entity was found targeting financial entities and was seen by the name Earth Lusca. Security researchers suspected Earth Lusca and APT41 has lot of similar attacking vectors and patterns, which raised a suspicion that they aren’t separate threat entities.
In the year 2020, the threat actors were linked to several intrusion campaign including Citrix NetScaler/ADC, ManageEngine Desktop Central, and Cisco Routers as these tools are widespread and can affected users across 20+ countries.
Attack vectors employed by Chinese APT41 hackers
As per Mandiant’s researchers, the vulnerabilities are zero-days in the USAHERDS application that is marked as CVE-2021-44207, the infamous Log4j marked as CVE-2021-44228 and named them to be ‘deliberate campaign’. The attackers are known for persistent attacks that involve the weaponization of abusing deserialization, directory traversal vulnerabilities, and SQL injection.
The Chinese APT41 hackers are known to be targeting both the public and private entities to perform espionage acts with financial gains. The recent act of these malicious actors include exploiting the Log4Shell vulnerability to gain access into targeted networks of two U.S state governments, a telecom firm and an insurance company.
Later, the hackers went ahead to deploy a new malware variant of modular C++ backdoor called KEYPLUG on Linux devices after harvesting and reconnaissance of those victim networks. Once successfully deployed, the next payload called DUSTPAN (aka StealthVector) is deployed for in-memory drop with advanced post-compromise tools like DEADEYE which launches the LOWKEY. APT41 hackers are fond of using Cloudfare services said the Mandiant researcher as the actors have been seen using the same attack orchestration techniques in multiple instances.
Chinese APT hackers and U.S Department of Justice
APt41 hackers have been on the most wanted list of the FBI as they have been accused of multiple Healthcare, High-tech, Financial and Telecom organizations over the years. APT31 and APT41 are very active recently and their prime targets are usually US organizations.
Subscribe to our newsletter for daily alerts on cyber events, you can also follow us on Facebook, Linkedin, and Twitter.
You can reach out to us via Twitter/ Facebook or mail us at admin@thecybersecuritytimes.com for advertising requests.








