Blister malware can breach your devices in absolute stealth

A new malicious campaign was discovered by security researchers that disguises malicious code as legitimate exe files. The researchers have figured out that there is a payload that is considered a novel threat and being distributed to Windows systems with a low detection rate called Blister.
The actors behind Blister malware have made their move sneaky by employing multiple techniques, the code-signing certificates are one among many techniques.
A brief study on Blister malware and its capabilities
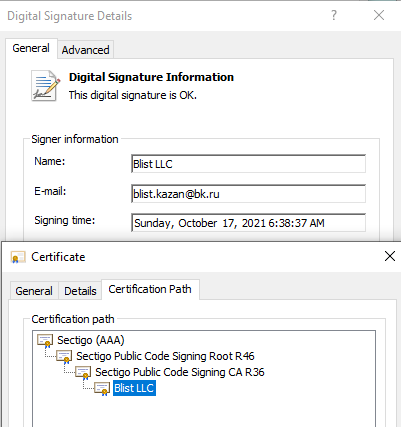
The actors behind Blister malware is found to be actively running this campaign for more than three months now, as per Elastic search company. The actors have used a code-signing certificate which is from Aug 23 and was issued by Sectigo for a company called Blist LLC.
Though usage of valid certificates to sign malware is a traditional trick as they were used to steal certificates from legitimate companies but now the attack vectors have improved as the actors get a valid certificate from a organization directly.
Elastic claims that they have reported this case with Sectigo, as the Blister malware disguises into a legitimate library along with other techniques to stay undetected.
Then elevated privileges are also added to the Blister malware using the rundll32 command, with valid certificate and administrator privileges will help Blister malware evade security solutions and sneak into the devices.
Protecting your network against Blister malware
After the sneaky penetration, Blister malware decodes from the bootstrapping code. The code is dormant for ten minutes to escape sandbox analysis.
Blister malware then starts decrypting embedded payloads which will allow lateral movement and remote access. The malware achieves persistence which will allow it to launch during startup by copying itself into the ProgramData folder as disguising itself as rundll32.exe.
Both signed and unsigned versions of Blister malware can have a reduced detection rate against antivirus software. With the combination of valid-code signing certs, disguised legitimate looking libraries with malicious codes, and payloads allowed the success rates of the attack.
Elastic company has published a Yara rule to detect Blister malware presence and provide the details of the malware to assist organizations prepare against it.
Subscribe to our newsletter for daily alerts on cyber events, you can also follow us on Facebook, Linkedin, Instagram, Twitter and Reddit.
You can reach out to us via Twitter or Facebook, for any advertising requests.





