Spain arrest threat actors for SIM Swapping Attack

The Policia Nacional has arrested eight individuals last week after dismantling an anonymous cybercriminals organization for several SIM swapping attacks and financial fraud.
Threat actors exploit bank accounts using SIM swapping attack
The cybercriminals disguised themselves as trustworthy representatives of banks and other financial organizations to perform phishing and smishing techniques to extract personal information and banking data before stealing money from the victims account.
“They usurped the identity of their victims through the falsification of official documents and tricked employees of telephone stores into getting the duplicate of SIM cards, cards where they received security confirmation messages from banks that allowed them to empty their victims’ accounts,” said the Spanish Police.
Out of the eight arrests seven of the actors were arrested in Barcelona and one in Seville. As per reports it is reported that 12 bank accounts were frozen as part of this operation. The first instance of breach was observed on March 2021.
What is SIM Swapping attack?
The technique where a hacker target mobile carriers to gain access to victim’s bank accounts, cryptocurrency and other sensitive information is called as SIM Swapping or SIM Hijacking attack. This SIM swapping attack is usually combined with insider threats, phishing and social engineering attacks.
In this attack, the hacker will impersonate a victim to trick the mobile career to switch the victim’s mobile number to a SIM card which is already in their control. On the other hand, this can be achieved by bribing an employee of the mobile carrier or manipulating the employees into downloading malware which is then used to break into systems and perform SIM swaps.
After the phone numbers are ported, the hackers leverage their identity to perform account resets, bypass SMS-based 2FA security and take control of the target’s online accounts.
An increase in SIM Swapping Attacks
In recent times, SIM Swapping attacks have increased enormously stealing millions of dollars from cryptocurrency wallets and bank accounts. In Nov 2021, U.S prosecutors convicted a UK national for SIM swapping attack stealing $784K worth of cryptocurrency.
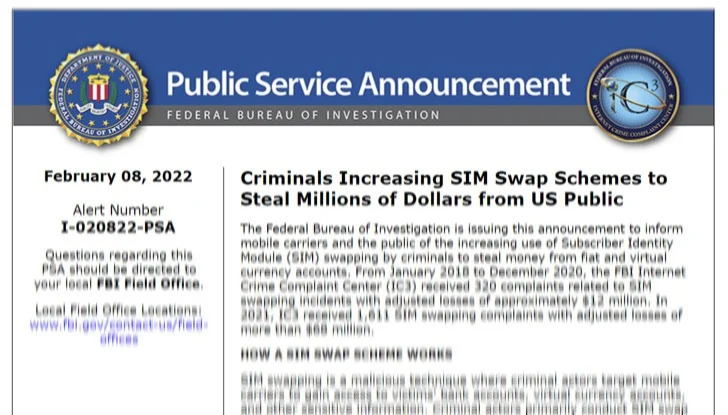
In 2021 from January to December, the FBI received 1611 SIM Swapping complaints with around $68 million in losses. And it was 320 from 2018 to 2020 with $12 million in losses.
Subscribe to our newsletter for daily alerts on cyber events, you can also follow us on Facebook, Linkedin, Instagram, Twitter and Reddit.
You can reach out to us via Twitter or Facebook, for any advertising requests.





