Samsung data breach by LAPSUS$ leak source codes and 190GB of data

Samsung has confirmed that the firm is hit by a security breach which has resulted in the exposure of internal company data, including the source code of its Galaxy Smartphones.
“According to our initial analysis, the breach involves some source code relating to the operation of Galaxy devices, but does not include the personal information of our consumers or employees,” Samsung told Bloomberg.
LAPSUS$ hackers take responsibility for Samsung data breach
The LAPSUS$ hacking group has leaked the breached data into a Telegram channel which confirmed the data breach publicly.
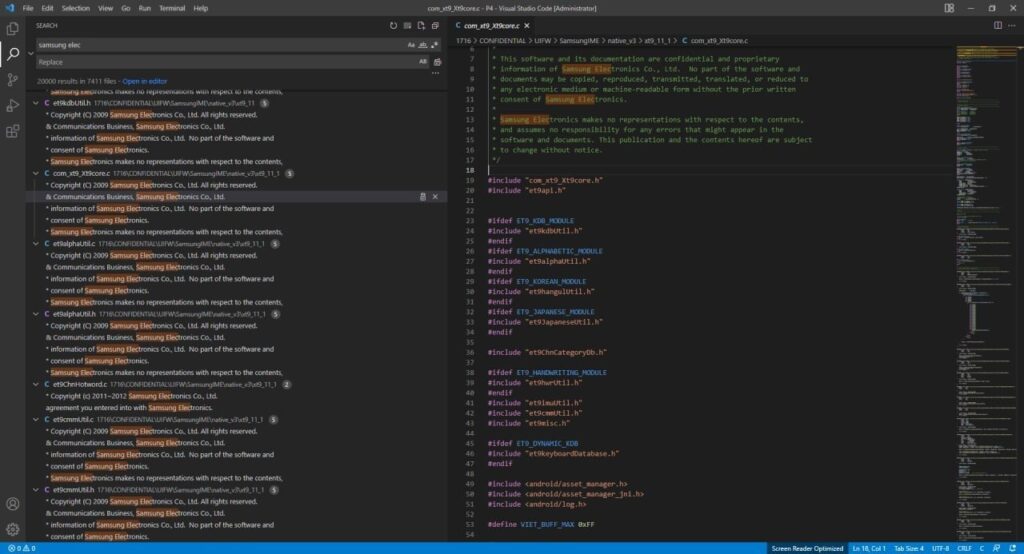
This Samsung data breach exposed the source code for trusted applets installed within TrustZone, biometrics authentication, confidential data from Qualcomm’s chip, source code for Samsung’s activation servers, full source code used for authenticating Samsung accounts, including services/APIs, and boot-loaders for recent devices.
LAPSUS$ hackers is also become recently popular for their breach on NVIDIA data breach that got away with 1TB trove of proprietary data including employee name, credentials, schematics, driver source code and other details related to latest graphic chips. The LAPSUS$ group was first seen in December 2021, and demanded NVIDIA to open-source its GPU drivers and remove Ethereum cryptocurrency mining cap from the Graphic card manufacturer’s 30-series GPUs.
The demands for Samsung data breach is not known yet but researchers predict it could be around similar lines.
Samsung data breach and the data leak by LAPSUS$
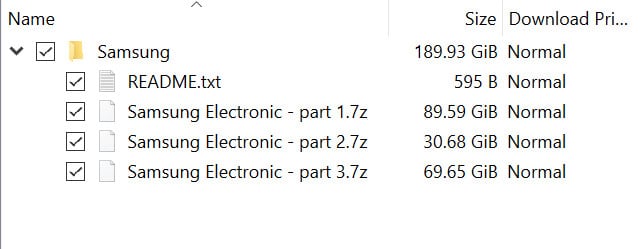
LAPSUS$ has classified the stolen data into three compressed files that counts a totla of 190GB and it is published in a torrent for popularity, and is now shared by more than 400 peers actively. LAPSUS$ is also in process of including more severs to increase the download speed.
The classification of the Samsung data breach information is as follows,
- Part 1: Contains the source code and data related to Security/Defense/Bootloader/TrustedApps/Knox.
- Part 2: Contains source code related to device security and encryption.
- Part 3: Contains several repositories of Samsung’s Github, Samsung account backend, Samsung backend/frontend, mobile defense engineering, and SES (Bixby, Smartthings, Store).
The South Korean company has confirmed that the data breach doesn’t affect its business and customers. They have also implemented appropriate measures to prevent such breaches in future.
Subscribe to our newsletter for daily alerts on cyber events, you can also follow us on Facebook, Linkedin, and Twitter.
You can reach out to us via Twitter/ Facebook or mail us at admin@thecybersecuritytimes.com for advertising requests.








