Russian Somnia ransomware group targets Ukrainian Organizations

A Russian malicious entity group is infecting multiple organizations in Ukraine with a new strain called Somnia Ransomware, encrypting the devices and affecting operations.
The Computer Emergency Response Team of Ukraine (CERT-UA) has announced the outbreak with attacks coming from Russia With Love (FRwL), also called as Z-Team also tracked as UAC-0118.
The group first created the Somnia Ransomware on Telegram and displayed proofs of attacks against the tank producers in Ukraine. However, Ukraine hasn’t confirmed the successful encryption attacks by the Somnia Ransomware operators.
Somnia Ransomware Attack details
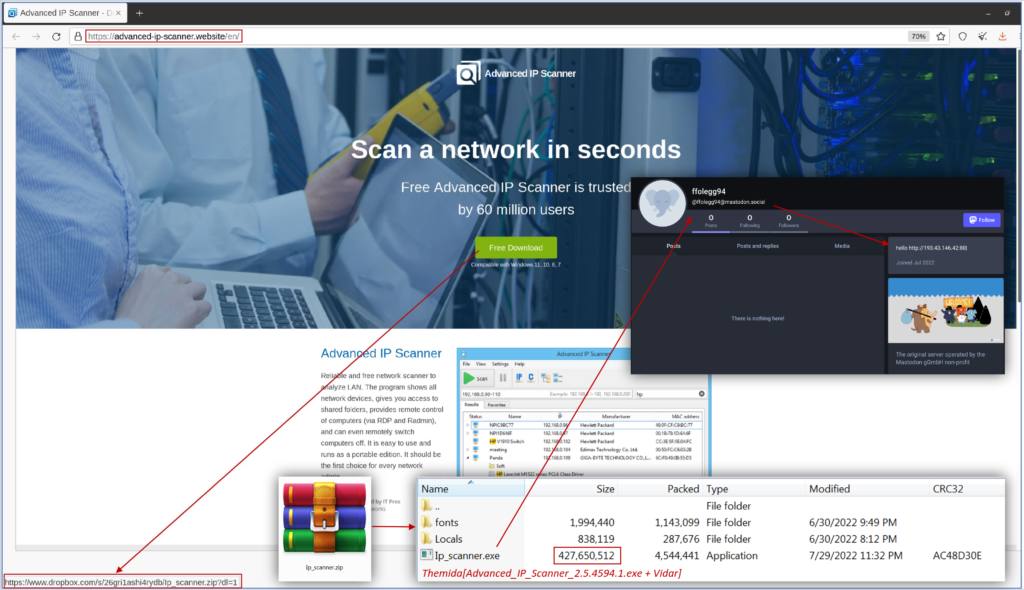
As per CERT-UA, the somnia ransomware uses malicious fake site that mimic the ‘Advanced IP Scanner’ to manipulate businesses and their employees by downloading an installer. T
his EXE file will affect the system with the Vidar Stealer, by taking over the session data to control infected user account
The Somnia Ransomware entity is abusing Telegram accounts to extract VPN connection data. If users didn’t configure 2FA, and hackers use it to gain unauthorized access to the victim’s corporate network.
After intruding the target devices, the malicious actors deploy Cobalt Strike beacon to exfiltrate data and use Netscan, Anydesk, Ngrok and Rclone for surveillance remote access activities.
CERT-UA reports that after Spring 2022, with help of initial access brokers, Somnia Ransomware operators executed several attacks on computers belonging to Ukrainian businesses. Also, the recent samples of Somnia ransomware were used in 3DES, relying on AES algorithm, using the symmetric 3DES.
Somnia Ransomware and its real motive
This is the list of file types infected by Somnia Ransomware – documents, images, databases, archives, video files and more. The ransomware injects the .somnia extension to the encrypted file’s names.
Unlike other ransomware, Somnia doesn’t request for a ransom but instead targeting the disruption of target operations rather than monetizing through the malicious act.
With this attribute of destruction, somnia ransomware will fall into the category of data wiper than just a encrypting ransomware.
Subscribe to our newsletter for daily alerts on cyber events, you can also follow us on Facebook, Linkedin, and Twitter.
You can reach out to us via Twitter/ Facebook or mail us at admin@thecybersecuritytimes.com for advertising requests.





