Russian Chinese hackers and ransomware operators working together

Security researchers have identified some unusual activities in Russian cybercrime forums, where Russians and Chinese hackers seem to be collaborating recently. This behavior was first observed in RAMP hacking forum, when Mandarin speaking actors started sharing tips, tricks and making conversations on attacks.
Russian Chinese hackers get-together
Based on a report from Flashpoint, RAMP members are now communicating in the forums using machine translated Mandarin and there is sudden spike of 30 new members from China in the forum community.
Researchers predict that Russian ransomware operators are establishing a collaboration with Chinese hackers to prepare some attacks against U.S entities, exchange exploits, malware or to hire talents. A user that goes by the name Kajit is the one who seems to have initiated this activity and the user also seems to be the admin of the RAMP forum. It is be noted that this unusual Russian Chinese hackers combo was also seen in XSS hacking forum.
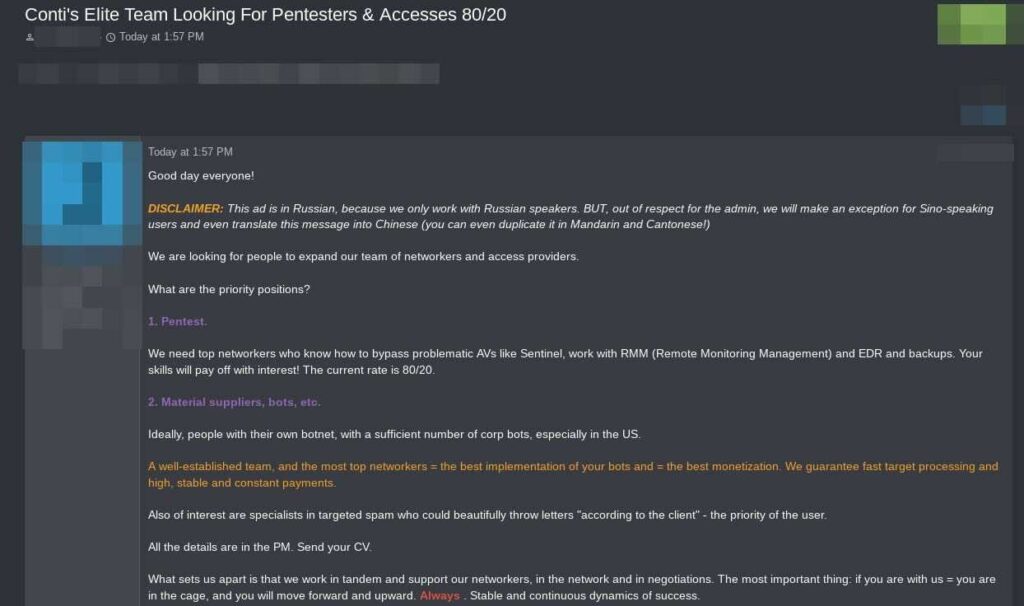
Recntly, one of the RAMP admin called as ‘boriselcin’ posted a topic calling on threat actors actors to attack the USA. Though these behaviors are a warning for the security professionals, it is also to be noted that most of the RAMP activities are a smokescreen and should be viewed with some skepticism.
“This ad is in Russian, because we only work with Russian speakers. BUT, out of respect for the admin, we will make an exception for Sino-speaking users and even translate this message in Chinese (you can even duplicate it in Mandarin and Canotonese!)”- Conti ransomware operation.
Hoax or not the infrastructure linked to Groove hosted data linked to at least a US police department and a NBA baseball team, so the victims are real. As the pressure increases on Ransomware actors we can expect more elaborate excuses, but in the end the evidence remains.
— John Fokker (@John_Fokker) November 3, 2021
RAMP is evolving
RAMP was established by a Babuk ransomware operator and since then this platform has been used to post stolen credentials and data from other cyberattacks performed, including vulnerabilities and payloads. One such data was exposed in September on Fortinet VPN with access to 12,856 devices and around 498K credentials.
Since its a holiday season in US, the security teams and professionals should be on high alert to stop something that is cooking in the RAMP and XSS forum. The recent Emotet Malware rebirth is another red light as well.
Subscribe to our newsletter for daily alerts on cyber events, you can also follow us on Facebook, Linkedin, Instagram, Twitter and Reddit.
You can reach out to us via Twitter or Facebook, for any advertising requests.