Robin Banks returns with stealth and can bypass MFA authentication

A Russian phishing-as-a-service platform called the Robin Banks is back again offering protection against distributed denial-of-service (DDoS) attacks.
What is Robin Banks?
Robin Banks is a phishing-as-a-service platform that faced disruption in July 2022, when IronNet researchers exposed the platform as anti-cyber activity platform as the phishing service targeted Citibank, Captial One, PNC, Wells Fargo, Bank of America, U.S.Bank, Santander, Lloyds Bank and the Commonwealth Bank.
After identifying the intentions of the platform another security firm called Cloudflare blacklisted the platforms’ backend and frontend, stopping their ongoing phishing campaigns from cybercriminals paying a subscription for the Phass platform.
A report from the IronNet researchers states that the PhaaS platform operators can return and are taking enough measures to hide their platform white hats.
The latest features include MFA and a redirector that facilitates stealth.
The all-new Robin Banks and its threats
The PhaaS platform is now working with a Russian internet services provider called DDoS Guard with a lot of controversial business exchanges.
With 2FA, Robin Banks is coming again with better stealth and validation protocols to keep the security researchers away from their interface and the communication between admins are via Telegram channel.
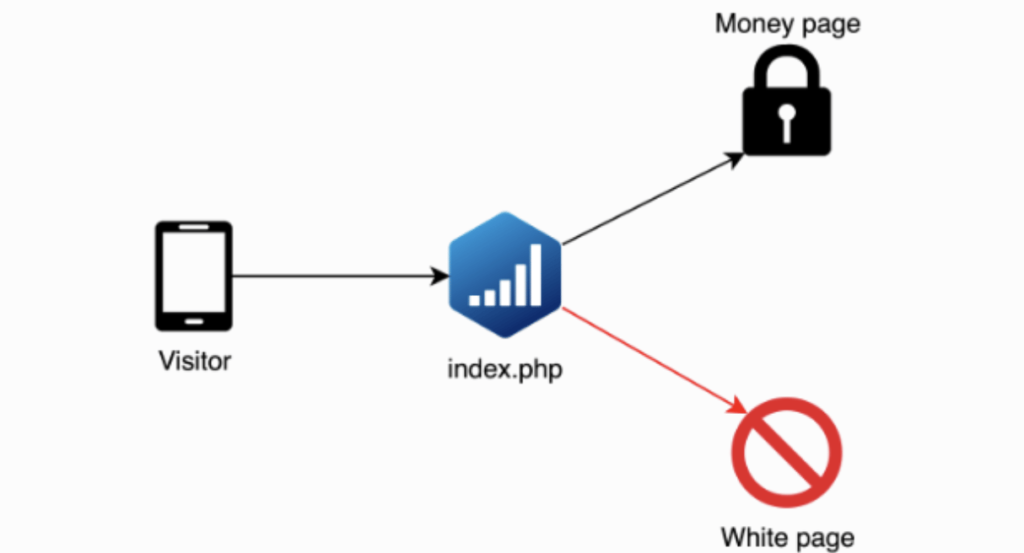
The stealth is made possible using a third-party cloakers, bot filter and adtracker.
With PhaaS platforms using tools like Adspect the site will redirect scanners and unknown traffic to benign websites, thus staying on stealth. The Robin banks sells its services on dark web forums and on Telegram channels.
Robin Banks and its MFA bypassing technique
The developers of Robin Banks have deployed the ‘Evilginx2’ for reverse proxy in adversary-in-the-middle attack to steal cookies containing authentication tokens.
Evilginx2 is a reverse proxy tool that is used for communicating between a victim and server, sharing credentials, login requests and capturing session cookies.
With the help of Evilginx the phishing platform Robin Banks will bypass the MFA system, capture cookies to login to an account as if they are the actual owners.
They then share this login info on Dark Web, Google, Yahoo and Outlook phislets. Considering the availability of such PhaaS websites, anyone with less technical knowledge can become cybercriminals, with power to launch phishing attacks on targeted entities and even bypass MFA to steal account credentials.
Only recently we made a post on SocGholish malware targeting more than 250 US sites and now this new PhaaS platform with enhanced steath and MFA bypass looks threatening.
Subscribe to our newsletter for daily alerts on cyber events, you can also follow us on Facebook, Linkedin, and Twitter.
You can reach out to us via Twitter/ Facebook or mail us at admin@thecybersecuritytimes.com for advertising requests.








