New Mars Stealer malware is distributed via Google Ads and OpenOffice

A new information stealing payload called ‘Mars Stealer malware‘ is increasing in popularity and threat analysts have spotted large scale campaigns are employing it. After analyzing it for a while, the Mars Stealer malware is a modified version of Oski malware that has info-stealing capabilities targeting broad spectrum of apps.
The malware is marketed in hacking forums for around $140-$160, and is seeing a decent growth in user counts, as the malware is similar to Racoon malware. And because of the growth this Mars Stealer malware can soon be seen in multiple hacking campaigns says the Threat Analysts at Morphisec Report.
Mars Stealer on a OpenOffice Campaign
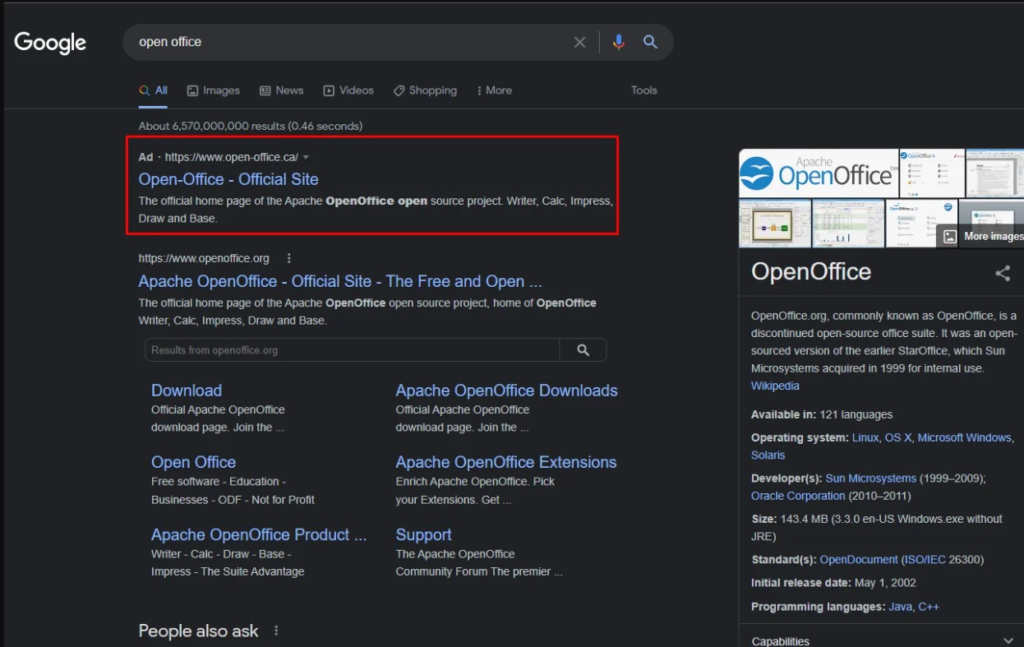
As per Morphisec report, a new campaign is already active and is using Google Ads advertising to rank the morphed OpenOffice sites high on Canadian Search Results. OpenOffice is quite popular among the free users and hits a massive download count everyday.
The threat actors have cloned the Mars Stealer malware as the OpenOffice installer with the Babadeda crypter or the Autoit loader so the targeted users will infect themselves by installing the OpenOffice which is the Mars Stealer in disguise.
Data Stolen by Mars Steaker malware
The active campaign distributing the Mars Stealer appears to steal the browser auto-fill data, credit card details, IP address, country code, browser extension details and timezone.
The funny thing about this campaign is that, the hackers mistakenly installed the Mars Stealer on their own system while testing it and this allowed the security researchers to map their GitLab accounts, credentials and Google Ad account details.
Mars Stealer threatening cryptocurrency
The operators that use Mars Stealer malware is targeting cryptocurrency assets. The browser plugin called MetaMask, followed by Coinbase Wallet, Math Wallet and Binance Wallet is the most stolen plugin. And the research firm Morphisec also found credentials that belonged to a healthcare infrastructure provider in Canada and has trace of high-profile Canadian service firms.
To keep your network and device safe against Mars Stealer malware, avoid Google Ad links. If you need complete technical details on the malware please find it here at 3xp0rt’s analysis.
Subscribe to our newsletter for daily alerts on cyber events, you can also follow us on Facebook, Linkedin, and Twitter.
You can reach out to us via Twitter/ Facebook or mail us at admin@thecybersecuritytimes.com for advertising requests.





