MoonBounce Bootkit targets UEFI hard drives making it irreplaceable

Security researchers from Kaspersky have discovered a novel bootkit that can infect UEFI firmware in a computer. This malware is found to be a novel one, can be troublesome if compromises your network devices.
What is MonoBounce bootkit?
MoonBounce is a novel bootkit malware that affects the SPI flaws memory that is found on the motherboard. It doesn’t reside the hard drive named ESP where the UEFI code typically resides. As per Kaspersky research, the defenders can’t reinstall the operating system to replace the hard drive as this MoonBounce bootkit will continue to exist in the Infective drive until the SPI memory or the motherboard is fixed.
MoonBounce is the third UEFI bootkit that has been discovered so far which can infect and reside within the SPI memory joining its predecessors MosaicRegressor and LoJox.
Also, the discovery of MoonBounce bootkit comes after other bootkit discoveries in recent months, including ESPectre, FinSpy’s UEFI bootkit and few others, which proves the release of UEFI standard was challenging for hackers before but not anymore.
The MoonBounce bootkit and Chinese APT41 connection
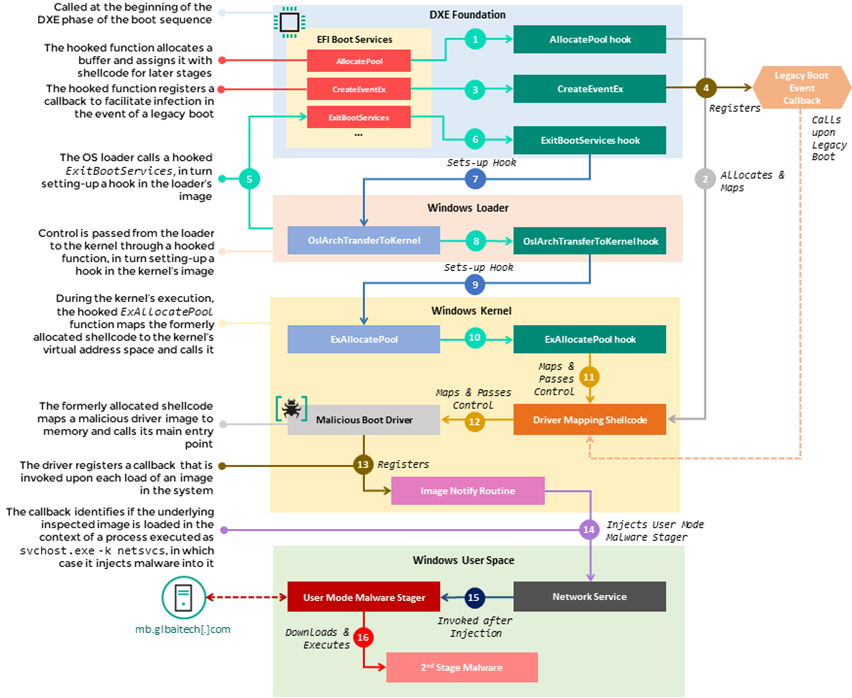
Kaspersky researchers mentioned that the MoonBounce bootkit will allow hackers to keep their access on infected devices and further deploy additional payloads for other motives. A Transportation Service company have had the strains of MoonBounce bootkit on their network and had deployed other payloads on to the company’s devices. Researchers had studied those payloads and have narrowed down China’s APT41 group to be the ones behind MoonBounce bootkit.
This connection with the cyber-espionage group APT41 was confirmed when both MoonBounce bootkit and other payloads were communicating with the same server infrastructure. Since the other payloads have been linked to APT41, the MoonBounce bootkit also must be theirs.
The mere question for the researchers is how MoonBounce bootkit was deployed into the devices in first place.
How to stay vigilant against MoonBounce bootkit?
Kaspersky researchers have asked users to update their UEFI firmware periodically to verify their BootGuard is in place and enabled. Also, Trust Platform Modules should be enabled for the respected hardware to ensure security against MoonBounce.
Subscribe to our newsletter for daily alerts on cyber events, you can also follow us on Facebook, Linkedin, Instagram, Twitter and Reddit.
You can reach out to us via Twitter or Facebook, for any advertising requests.





