IsaacWiper and HermeticWiper malware compromises Ukrainian organizations

A new data wiper malware called IsaacWiper has been identified in Ukrainian government network recently. Multiple cyberattacks are happening in Ukraine and Russia due to the ongoing Russian invasion of Ukraine.
Slovak cybersecurity firm ESET identified the new malware ‘IsaacWiper‘, and was found in the Ukrainian network on Feb 24th which wasn’t infected by HemeticWiper aka Foxblade malware.
Foxblade is another data wiper that was deployed targeting Ukrainian organizations recently. The motive behind either of these malware threats is to sabotage the infected network and shutting down the machines associated with them.
Modus operandi of IssacWiper and HermaticWiper malware
The HermeticWiper attack affected five Ukrainian organizations, and is found to own worm-like behavior that distributes itself across the compromised network and has a ransomware abilities. HermeticWiper can be a decoy ransomware as it can even wipe the data and not just encrypt it. HermeticWiper can also erase itself from the affected device in the disk by overwriting its own file with random bytes.
As of now the threat actor associated with this malware threat has not been identified and the behavior shows the intrusion has been in plans for several months now.
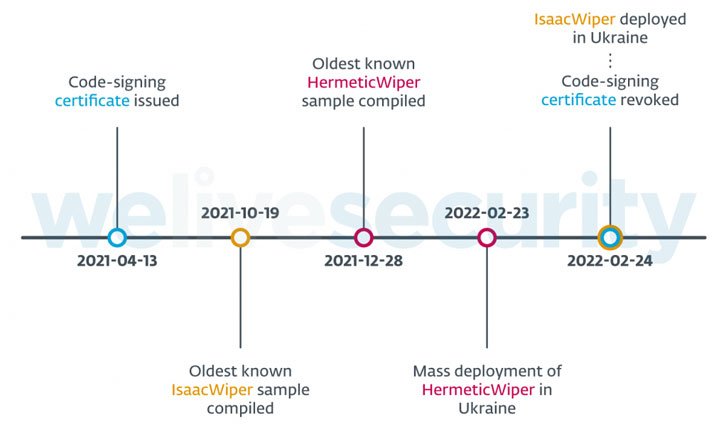
The oldest timestamp for HermaticWiper was found to be on Dec 28,2021, and had code-signing certificate with April 13, 2021 date on it. All this shows, the threat actors had access to the network and the Active Directory servers for a prolonged time.
As per ESET, attackers have exploited tools like Impacket and RemCom, remote access software to breach the network, lateral movement and malware distribution.
On the other hand, IsaacWiper isn’t identical to HermeticWiper in its code and is found to be less sophisticated. Later on Feb 25th, attackers updated the IsaacWiper with debug logs to wipe the infected system as the primary version wasn’t capable of achieving it.
Considering the escalating tensions between Ukraine and Russia in recent days, the cyberattacks are only expected to rise for either side. The Ukraine has also set up an IT army to be more cyber active against Russia during these unprecedented times. Both IssacWiper and HermaticWiper can continue to affect Ukrainian infrastructure until the root cause of these malware are identified and rectified.
Subscribe to our newsletter for daily alerts on cyber events, you can also follow us on Facebook, Linkedin, Twitter, and Reddit.
You can reach out to us via Twitter/ Facebook or mail us at admin@thecybersecuritytimes.com for advertising requests.








