Hackers exploiting SolarWinds Serv-U by leveraging the Log4j vulnerability
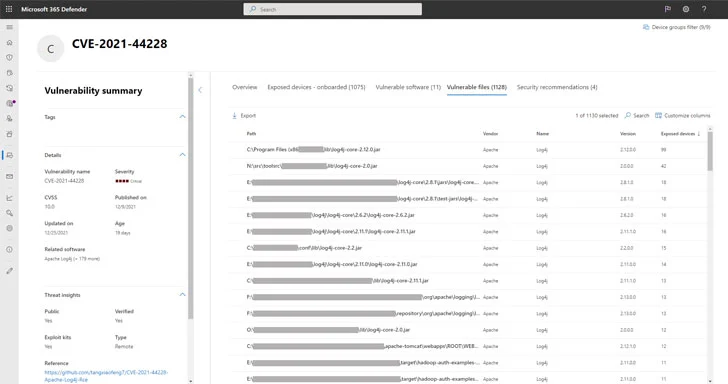
Microsoft disclosed details of a new security vulnerability with SolarWinds Serv-U software that is found to be leveraged by threat actors to launch attacks by exploiting the Log4j flaws to breach networks.
The vulnerability tracked as CVE-2021-35247, “the issue is input validation vulnerability that will allow attackers to build a query given some input and send that query over the network without sanitation” said Microsoft Threat Intelligence Center (MSTIC).
SolarWinds Serv-U vulnerability and the advisory
The flaw in Serv-U versions 15.2.5 and prior was identified by Jonathan Bar Or, security researcher and the same has now been fixed in Serv-U version 15.3.
SolarWinds advisory mentioned that the Serv-U web login screen to LDAP authentication was allowing characters that were not sufficiently sanitized. The fix will update the input mechanism to perform additional validation and sanitzation.
IT management vendor also mentioned that the LDAP server had ignored improper characters which is they there isn’t any negative effect. However, Microsoft isn’t sure whether the attempts exploiting the Log4j vulnerability on SolarWinds Sev-U software is just an attempt or a successful attack.
SolarWinds Serv-U exploitation in the wild
We already knew that threat actors are actively exploiting Log4Shell vulnerability in mass and breaching networks to deploy backdoors, cryptominers, ransomware, and remote shells to gain access and for further manipulation of the network and devices. The flaw is also found to be exploited by Mirai Botnet for deploying malware said the Akamai researchers.
Also, a chinese hackers have previously exploited the critical security vulnerability affecting SolarWinds Serv-U (CVE-2021-35211) deploying nefarious programs on target devices.
Subscribe to our newsletter for daily alerts on cyber events, you can also follow us on Facebook, Linkedin, Instagram, Twitter and Reddit.
You can reach out to us via Twitter or Facebook, for any advertising requests.





