D-Link Data Breach: Source Code and Data Compromised

Taiwanese networking equipment manufacturer D-Link has acknowledged a recent data breach connected to information stolen from its network, which has been offered for sale on BreachForums.
The attacker claims to have obtained the source code for D-Link’s D-View network management software and millions of records containing personal information of customers and employees, including details about the company’s CEO. The stolen data encompasses names, emails, addresses, phone numbers, account registration dates, and the users’ last sign-in dates.
D-Link Data Breach results in theft of Personal Data and Source Code
The threat actor presented 45 stolen records, dating between 2012 and 2013, to validate the breach. Notably, the data appeared outdated.
The attacker revealed, “I have breached the internal network of D-Link in Taiwan, I have 3 million lines of customer information, as well as source code to D-View extracted from the system. This does include the information of MANY government officials in Taiwan, as well as the CEOs and employees of the company.”
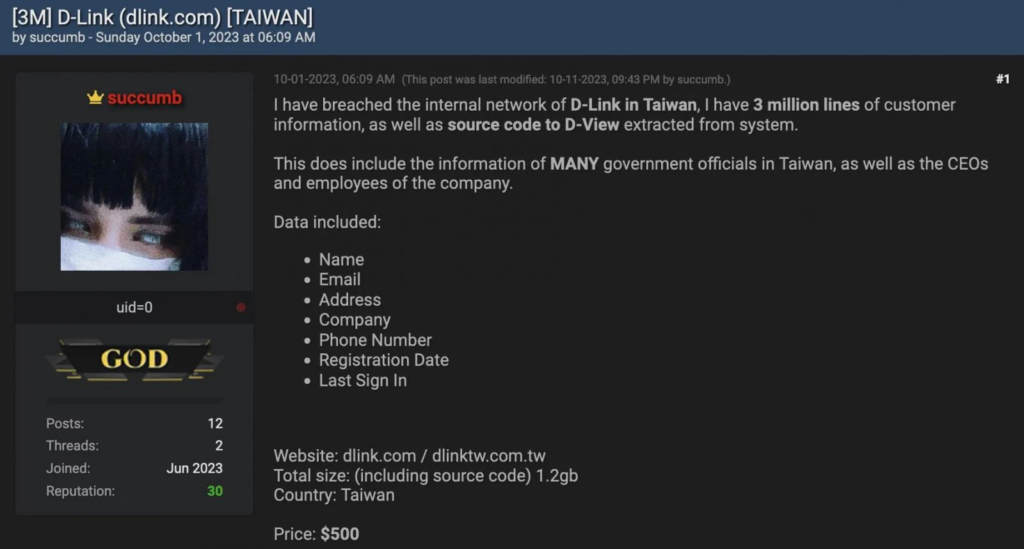
The compromised data has been available for purchase on the hacking forum since October 1st, with the threat actor demanding $500 for the stolen customer information and the alleged D-View source code.
D-Link has attributed the security breach to an employee falling victim to a phishing attack, which provided the attacker access to the company’s network.
In response, the company swiftly shut down potentially affected servers and disabled all but two user accounts used during the investigation.
While confirming the breach, D-Link clarified that the intruder accessed a product registration system within a “test lab environment,” operating on an outdated D-View 6 system that reached its end of life in 2015.
Breach Details, Company Response, and Minimal Impact on Customers
The reason for keeping an end-of-life server operational on D-Link’s network, potentially exposed to the internet for seven years, remains uncertain.
Contrary to the attacker’s claim of stealing millions of users’ data, D-Link revealed that the compromised system contained approximately 700 records, pertaining to accounts that had been inactive for at least seven years.
The company stated, “Based on the investigations, however, it only contained approximately 700 outdated and fragmented records that had been inactive for at least seven years.” Most of the data comprised low-sensitivity and semi-public information.
D-Link also suspects that the threat actor intentionally manipulated recent login timestamps to create the illusion of a more recent data theft. Additionally, the company reassured that the majority of its existing customers are unlikely to be affected by this incident.








