Coronavirus ransomware encrypts devices to secretly allow Kpot steal credentials

A new ransomware variant called ‘Coronavirus’ is distributed through a bogus website Wisecleaner.best , pretending as if it is recommending device optimization software. With the panic around the coronavirus outbreak becoming worse everyday, a hacker has specially packaged two malware and distributed this using this fake website.
First discovered by MalwareHunterteam, this coronavirus ransomware was studied and analyzed to have inherited wiper like characters as well. Attackers have created the Wisecleaner site, which looks exactly like the Windows system utility site Wisecleaner.com (another example of Phishing scam) and contains a file named WSHSetup.exe which will trigger the download of the coronavirus ransomware and info-stealer malware Kpot. Once the execution begins, two different files are downloaded, the file1.exe which downloads the Kpot info-stealer and the file2.exe that downloads the coronavirus ransomware.
What is Kpot malware?
Kpot can steal passwords from browsers, messaging applications, VPNs, gaming accounts like Stream and also steal cookies. It can also fetch information from FTP communication and other login credentials. Kpot has some extra perks that hackers can utilize, like sharing screenshots of the infected computer and getting away with cryptocurrencies from the victim computers.
What is coronavirus ransomware?
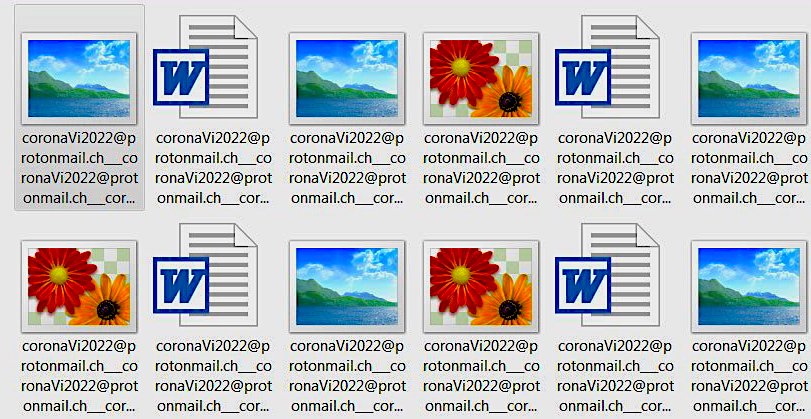
Like any other ransomware, this one encrypts 50 different formats of files in users machines and renames it with ‘coronaVi2022@protonmail.ch___1.jpg’ and in some cases it sends the email in loops to name the files. After encrypting the files, the coronavirus ransomware asks for 0.008 bitcoin as the ransom which is approximately $50. And to spice things up it also renames the C: drive as a coronavirus.
How is coronavirus different from other ransomware variants?
Other ransomware’s primary intentions were to encrypt files and ask for ransom, once paid hackers would share the encryption key or they may not. On the contrary, this ransomware is found to retain wiper attributes meaning it can delete the encrypted files anytime and also the ransomware comes with a info-stealer malware which may sustain in the infected computer making it look tiny compared to the Coronavirus encryption. However, this Kpot malware can steal cookies, login credentials, and more for long time, it can totally spy on the users using its spyware kinda attributes making the threat critical comparatively. Last month we did discuss about another info-stealing malware called ‘Raccon‘ which stole data from 60 different applications.
Users are advised to stay aware of this bogus Wisecleaner website and for those who have been infected by this strain please ensure your have updated your credentials from a different system before it is too late. While most of the ransomware exploits a vulnerability in a system or network this strain is none of that type, hacker crafts a website and distributes the malware so anyone can become a victim to this threat, thus stay alert.
Subscribe to ‘The Cybersecurity Times’, for daily alerts on cyber events. You can also follow us on Facebook, Linkedin, Instagram, Twitter and Reddit.