Coca-Cola’s network may have been compromised by Stormous Hackers

Coca-Cola, the world’s major soft drinks manufacturer confirmed that a cyberattack reported on its network is suspected and is currently investigating the same. The US -based giant is investigating the Stormous hackers that has claimed to have breached into the company’s servers and have stolen around 160GB of corporate data.
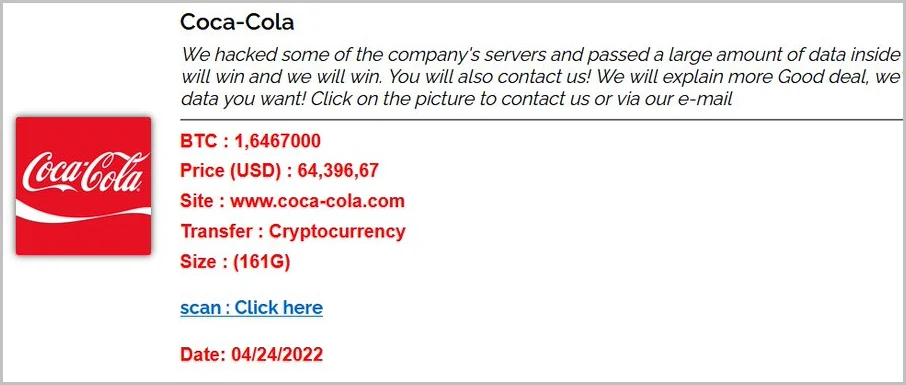
The hackers have also mentioned that they own data from the company’s cache and is being listed on their site asking for 1.65 Bitcoin which is $64,000. The listed files include compressed documents, text files, passwords, emails, account and payment ZIP archives.
What is Stormous, Who are the Stormous hackers?
Stormous is a hacking group that is claiming themselves to be ransomware operators. However, as of now, no file-encrypting malware has been deployed by the Stormous hacking group. The group also mentioned that they will take action against any hacking entities that’s targeting Russia. They also have published those extorted data on their site and have asked for votes to target their next victim.
The Stormous group promised DOS, leaking source code, and other business data when they breach a victim network. They also mentioned it only took a few days for them to breach into Coca-Cola’s network. It also to be noted that Epic Games were also targeted by Stormous before Coca-Cola, so it looks like the group is against the west.
The fairy tale between Coca-Cola and Stormous Hackers
As per the Stormous group they had breached and stolen data of 200 GB from Epic Store that belongs to 33 million users. However, all these claims haven’t been confirmed so their legitimacy is still a question until unless confirmed. Coca-Cola is working with law enforcement agency and their internal investigation team to confirm the same, but so far it seems negative and there is no impact on Coca-Cola’s network.
Subscribe to our newsletter for daily alerts on cyber events, you can also follow us on Facebook, Linkedin, and Twitter. You can reach out to us via Twitter/ Facebook or mail us at admin@thecybersecuritytimes.com for advertising requests.








