Citrix Bleed Vulnerability: A Critical Information-Disclosure Issue Sees Mass Exploitation

Security teams have raised the alarm as the Citrix Bleed vulnerability, a critical information-disclosure bug affecting NetScaler ADC and NetScaler Gateway, is now being exploited on a large scale. Thousands of Citrix NetScaler instances remain exposed to this threat, and the situation is concerning.
Citrix Bleed Vulnerability: 1000s of Vulnerable Servers Detected
As of October 30, security organization Shadowserver identified over 5,000 vulnerable servers on the public internet. Additionally, GreyNoise observed 137 individual IP addresses attempting to exploit the Citrix vulnerability in the past week.
Patch Release and Persisting Challenges
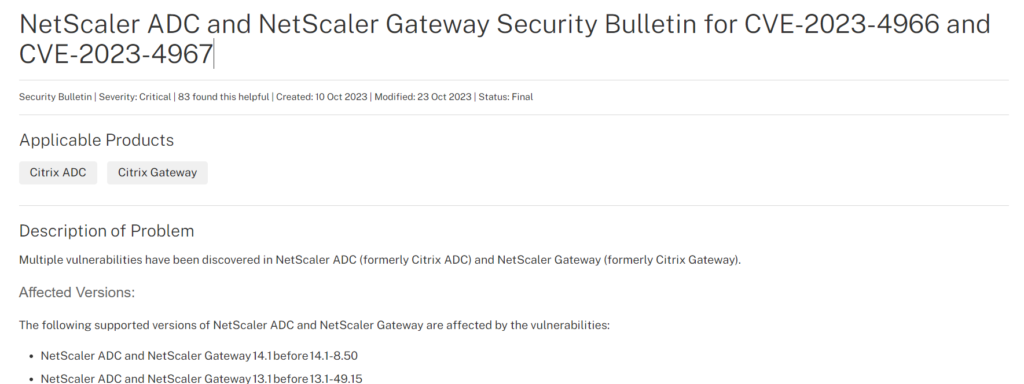
Citrix acknowledged the issue and released a patch for the flaw, known as CVE-2023-4966, on October 10. However, merely applying the patch and rebooting the system isn’t sufficient, as session tokens continue to pose a risk. Experts warn that session tokens can be exploited even after patching, emphasizing the severity of the problem.
Ransomware Gangs Targeting the Vulnerability
The “mass exploitation” of this vulnerability has attracted the attention of at least two ransomware gangs, as of October 30. These criminals are distributing a Python script to automate the attack process, making it a significant threat. Essentially, this situation exposes a vulnerability reminiscent of 1998 in remote access solutions, and attackers are collecting session tokens like prized possessions.
Exploitation Across Multiple Sectors
Security firm Mandiant revealed that it is currently tracking four separate groups exploiting the vulnerability in various sectors, including legal and professional services, tech, and government agencies across regions such as the Americas, Europe, Middle East, Africa, and Asia-Pacific. The exploitation is widespread and affects numerous sectors.
Assessing Exploitation within Organizations
Mandiant identified various ways to check for exploitation within organizations’ networks. However, it’s crucial to understand that patterns of suspicious activity related to session hijacking may vary from one organization to another. Therefore, the outlined techniques might not be universally applicable or feasible.
Response from Cybersecurity Authorities
The US government’s Cybersecurity and Infrastructure Security Agency (CISA) added CVE-2023-4966 to its Known Exploited and Vulnerabilities Catalog. However, the vulnerability is still listed as “unknown” in the “used in ransomware campaigns” category, despite ongoing exploitation.
Corporate Data Theft and Financial Motivations
Criminals have been exploiting this vulnerability since late August, initially limited to cyber espionage. Mandiant Consulting CTO Charles Carmakal anticipates that other threat actors with financial motivations will increasingly exploit this flaw over time, highlighting the urgency of addressing the situation.








