Amazon founder’s iPhone is hacked using the Saudi Prince’s What’sApp account

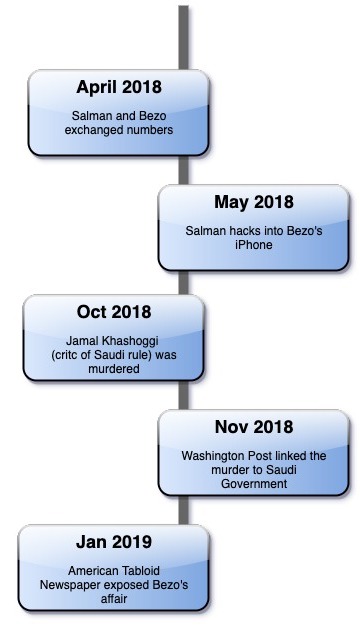
Jeff Bezos, the founder of Amazon and the world’s richest man’s iPhone was hacked on May 2018. Bezos received a MP4 file in his WhatsApp account from the Saudi Prince Mohammad Bin Salmon. Moreover, this hack was left undetected for a couple of months according to the Guardian and the Tabloid newspaper. It is also believed huge amount of data was extracted from Bezos phone since the hack.
How was Bezos phone hacked?
According to the digital forensics report, a malicious MP4 file was sent from Salmon’s account to Bezos which triggered the hack using an undisclosed zero day vulnerability in WhatsApp.
However, after escalating things with the United Nations Human Rights Office of the High Commission, it is identified the hack was executed using a mobile hacking tool called Pegasus, developed by Israeli vendor NSO Group.
Pegasus and its misuse
According to reports from the Amnesty International, Pegasus is misused by Saudi government to spy on Saudi dissidents. It is also reported that Pegasus was used to target human rights activists and journalists and attempted to install spyware on their smartphones. Also, two former employees of Twitter were charged for spying on the number of Twitter users on behalf of the Saudi government.
Moreover, it is also possible that the Prince’s phone could have been already hacked to execute the MP4 file hack on Bezos phone.
What was revealed post hack?
Massive amount of data egress had occurred, starting from 29,156 percent to 106,032,045 percent, i.e 126 MB to 4.6 Gb of data had been found extracted, however the details of data remains unknown. But on the other note Bezos affair disclosure could have been possible through this hack, as the hack did occur prior to it.
However, the Saudi government had dismissed the Guardian reports to be ‘absurd’ and have requested for further investigations. It is also to be noted that Bezos is also the founder of Washington post.
There was no information available regarding the leak of any official Amazon data from the hack of Bezos phone when this article was written. It is believed that after further forensic analysis, more information on the hack could be discovered.





